ITEA Cyber Security Advisory Board
To create a dialogue between Cyber Security customers and innovative Cyber Security technology providers, ITEA has established the Cyber Security Advisory Board.
This Advisory Board will serve its members to share immediate needs to experts of technologies in the ITEA Community, receive advice on the innovation and digital technology trends regularly, validate and shape any potential Cyber Security products that are being developed in an ITEA project, access the newest products that are developed in ITEA projects and discuss issues with other Cyber Security customers.
This Advisory Board will serve the ITEA Community to understand the urgent needs of Cyber Security, validate their potential products that are developed in ITEA projects and their features at an early stage and exploit their products to Cyber Security customers at the end of an ITEA project
The aim of the CySAB portal is to bring the Cyber Security challenges and innovative Cyber Security-related solutions of the CySAB members and the ITEA Community together in one place.
Participating CySAB organisations
Members
ASSA ABLOY AB
Tomasz Grabowski
Armengaud Innovate GmbH
Eric Armengaud
Ericsson
Ömer Faruk Tuna
Ford Otosan
Safa Çalışkan
Koç Finansman A.Ş
Zühal Dilek Ataman
NXP SemiConductors Belgium NV
Joppe Bos
PAL Robotics
Francesco Ferro
Saab
Johan Tenggren
Siemens AG
Andres Gonzalez Guilarte
Signify Netherlands B.V.
Sandeep Kumar
Turkcell Teknoloji
Emin Islam Tatli
Vitarex Studio Ltd
Gabor Gulyas
Cyber Security challenges
The ITEA CySAB meets twice a year: one meeting focuses on sharing the needs and challenges of the customers, and the second meeting focuses on sharing Cyber Security innovations resulting from the ITEA RD&I Community. The challenges shared in the first meeting are gathered in a report:
- Cyber Security Advisory Board - Meeting report June 2024
- Cyber Security Advisory Board - Meeting report July 2023
- Cyber Security Advisory Board - Meeting report July 2022
- Cyber Security Advisory Board - Meeting report July 2021
Latest Cyber Security-related news

Published on 06 Aug 2024
MTP invites companies to join proof of concept for AI-driven IoT detection in encrypted networks

Published on 05 Jul 2023
MTP implements Artificial Intelligence to detect IoT attacks
Find an overview of all Cyber security-related news in the news overview.
Cyber Security solutions e-Catalogue
If you wish to promote your Cyber security products / services that (partly) result from an ITEA project on this portal, please fill in the following form and send it to mathijs.van.dijk@itea4.org.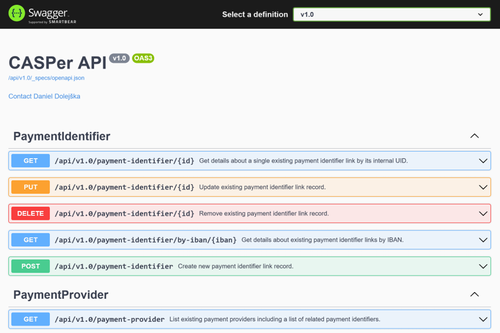
CASPer
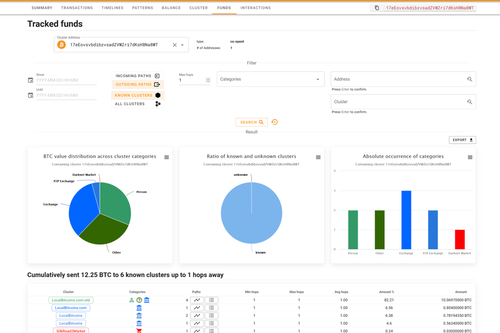
COINOMON
Unique features compared to the products by competition:
1) on-premises installation;
2) free API for integration with other tools/services;
3) OSINT and network intelligence enhancing information about address/cluster (meta)data.
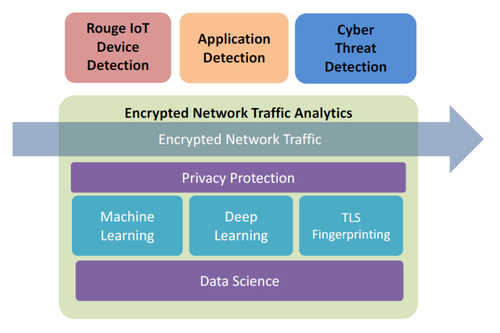
ENTA Solution
This solution allows to detect cyber-attacks hiding in encrypted traffic. Specifically, this solution covers:
• Detect rogue IoT devices
• Detect cyberattacks
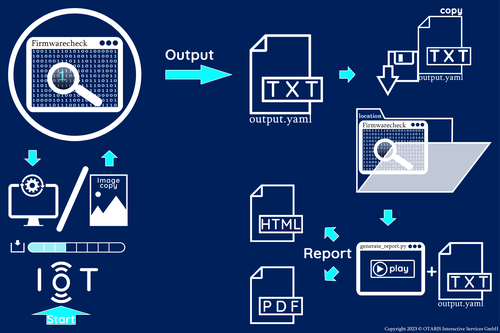
FirmwareCheck
- Outdated components (CVEs)
- Open (debug) ports
- Default passwords or anonymous logins
- Processes running as root
- Executables that can be used to get a reverse shell on a device

Irdeto Keys & Credentials

PRIGM Hardware-based cyber resilience solution
Find an overview of all Cyber Security-related solutions in the solutions
overview.
ITEA Cyber Security projects
Safety and Security is one of the main challenges of ITEA and therefore there are many ITEA projects solving different Safety and Security challenges, including Cyber Security. Below you can find more information about these Cyber Security-related ITEA projects:



IML4E
Industrial Machine Learning for Enterprises


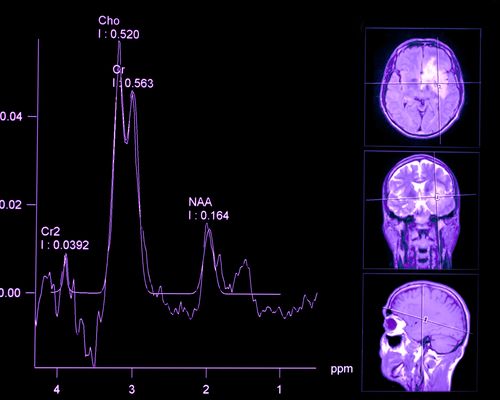
Spectralligence
Spectral Analysis in life sciences and materials sciences through Artificial Intelligence





DEFRAUDify
Detect Fraudulent Activities in dark web and clear web to protect your business







CyberFactory#1
Addressing opportunities and threats for the Factory of the Future (FoF)
For an overview of all Smart City-related projects, go to the full project list.
Cyber Security events
For an overview of all Cyber Security-related events, go to the full event
list.
Part of a bigger story
The ultimate goal is of the Cyber Security Advisory Board is to create a dialogue between Cyber Security customers and new Cyber Security technology developers
- As outcome of the CySAB meetings a Cyber Security challenges report will be written, that will be shared with the ITEA RD&I Community.
- The ITEA Community will pick up the challenges and create project ideas and corresponding project that will be shared in the ITEA Project idea tool. CySAB members are invited to check out these ideas and join those of their interest as use case providers.
- These Cyber Security-related project ideas and their corresponding consortia can be further defined during the ITEA Project Outline (PO) Preparation Days in September. CySAB members are invited to particpate in this event.
- Cyber Security-related project proposals can be submitted in the upcoming ITEA Call for projects in November.
- Successful Cyber Security-related proposals will receive a label in March of the next year and could be funded and start by the end of that year.